In a previous article we talked about how to perform digital forensics testing of RAM using Volatility framework. But we didn't talk about how we can acquire Random Access Memory (RAM) for a digital forensics test.
Here we use FTK Imager (Forensic Toolkit Imager) for our memory capturing job. We can install on a Windows computer (latest version of FTK Imager 4.5 comes for Windows only). After that we can acquire RAM.
FTK Imager can acquire primary storage systems also, but there are lots of article there in the internet about it. Here we are going to about how we can acquire a system's volatile memory (RAM) for forensics purpose.
First of all we need to download the latest FTK Imager tool from the official website https://accessdata.com/product-download/ftk-imager-version-4-5.
After clicking on "Download Now" we got a page to fill up a form and we need to put our mail-id there and then the download link will be mailed to us as we can see the following screenshot:
Here we can click to "Download FTK Imager" button. We need to click here then the download process will be started. This will be a less than 50MB exe file.After downloading we can install it as other Windows applications. Then we just need to run it as an administrator, shows in the following screenshot:
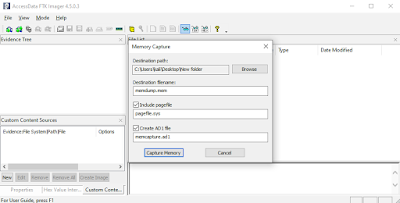
Then FTK Imager will open in front of us as we can see in the following screenshot:After this we click on the "File" located top left corner. Then we click on "Capture Memory" in the drop down menu. Showed in thee following screenshot:Then a popup box will open, here we can browse the destination folders path, where we want to save the acquired memory dump. Shown in the following screenshot:
After choosing the output folder we need to check (✅) for pagefile and AD1 file.
Then we just need to click on "Capture Memory" and the memory acquiring will started. Shown in the following screenshot:
After finishing the memory acquiring it will start capturing pagefile and AD1 file, as the following screenshot:Once the acquisition is completed, we can click on the "Close" button, as shown in the following screenshot:
Now we are Done. We can see the output files on our selected destination folder.
Now we can easily test this .mem file using Volatility on Kali Linux machine. We had talked about Volatility and it's uses previously.This is how can capture RAM for forensics testing. RAM's data is very volatile, when there are no electrical charge or current in the RAM chip. With the data on RAM being the most volatile, it ranks high in the order of volatility and must be forensically acquired and preserved as a matter of high priority.
Love our articles? Make sure to follow us on Twitter and GitHub, we post article updates there. To join our KaliLinuxIn family, join our Telegram Group. We are trying to build a community for Linux and Cybersecurity. For anything we always happy to help everyone on the comment section. As we know our comment section is always open to everyone. We read each and every comment and we always reply.